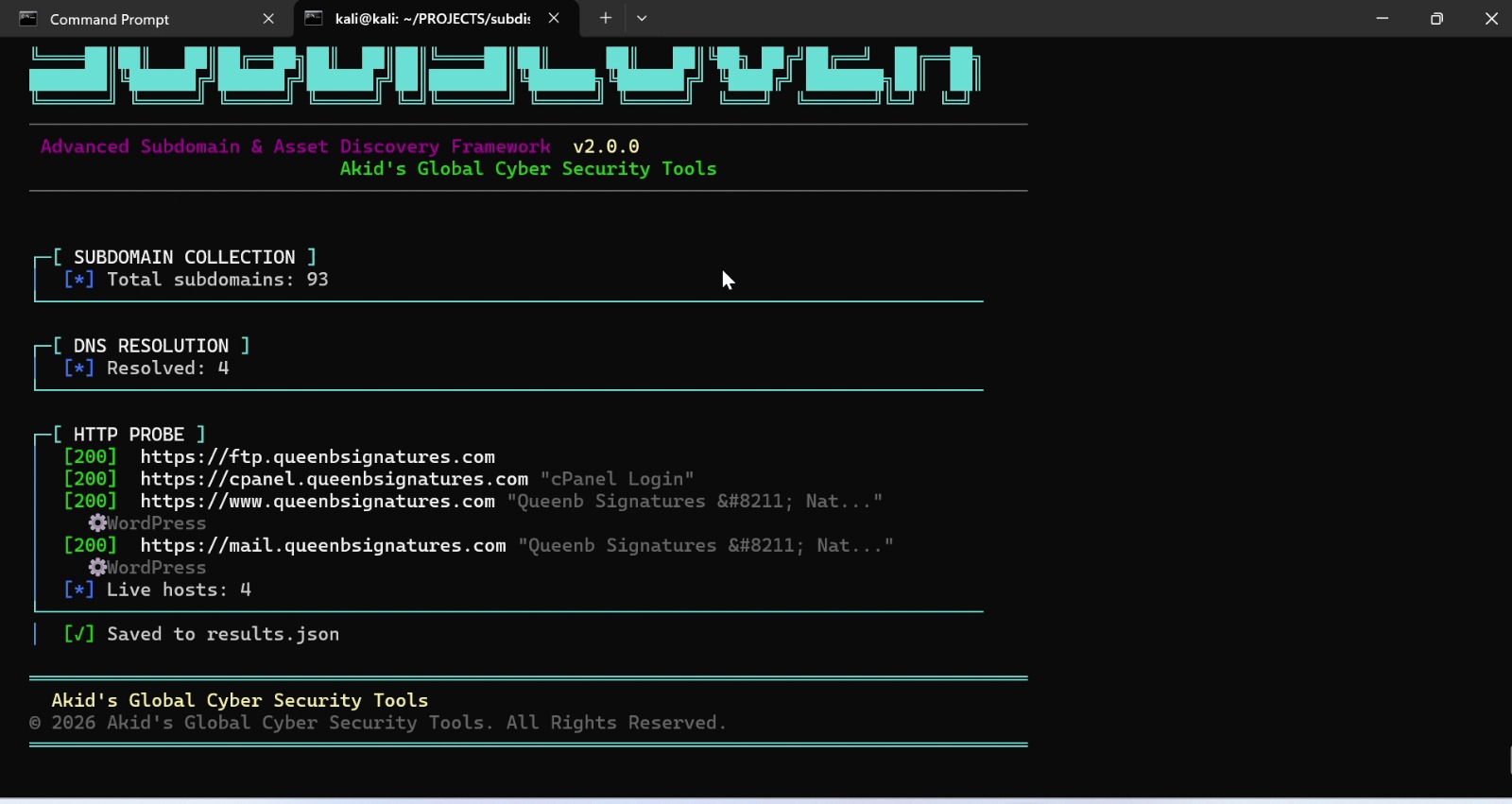
SubDiscover v2.0
SubDiscover v2.0 is an advanced subdomain and asset discovery engine written in Go, designed for authorized security testing. It combines multiple collection techniques including DNS...
IT Security Management | Cybersecurity & Malware Analysis | Risk Assessment | Incident Response

I am a seasoned cybersecurity expert with over a decade of experience in IT Security Management, Malware Analysis, Risk Assessment, and Incident Response. My mission is to protect organizations from evolving cyber threats through proactive defense strategies and cutting-edge research.
Specializing in threat intelligence, penetration testing, and digital forensics, I have successfully defended critical infrastructure, financial systems, and enterprise networks against sophisticated adversaries.
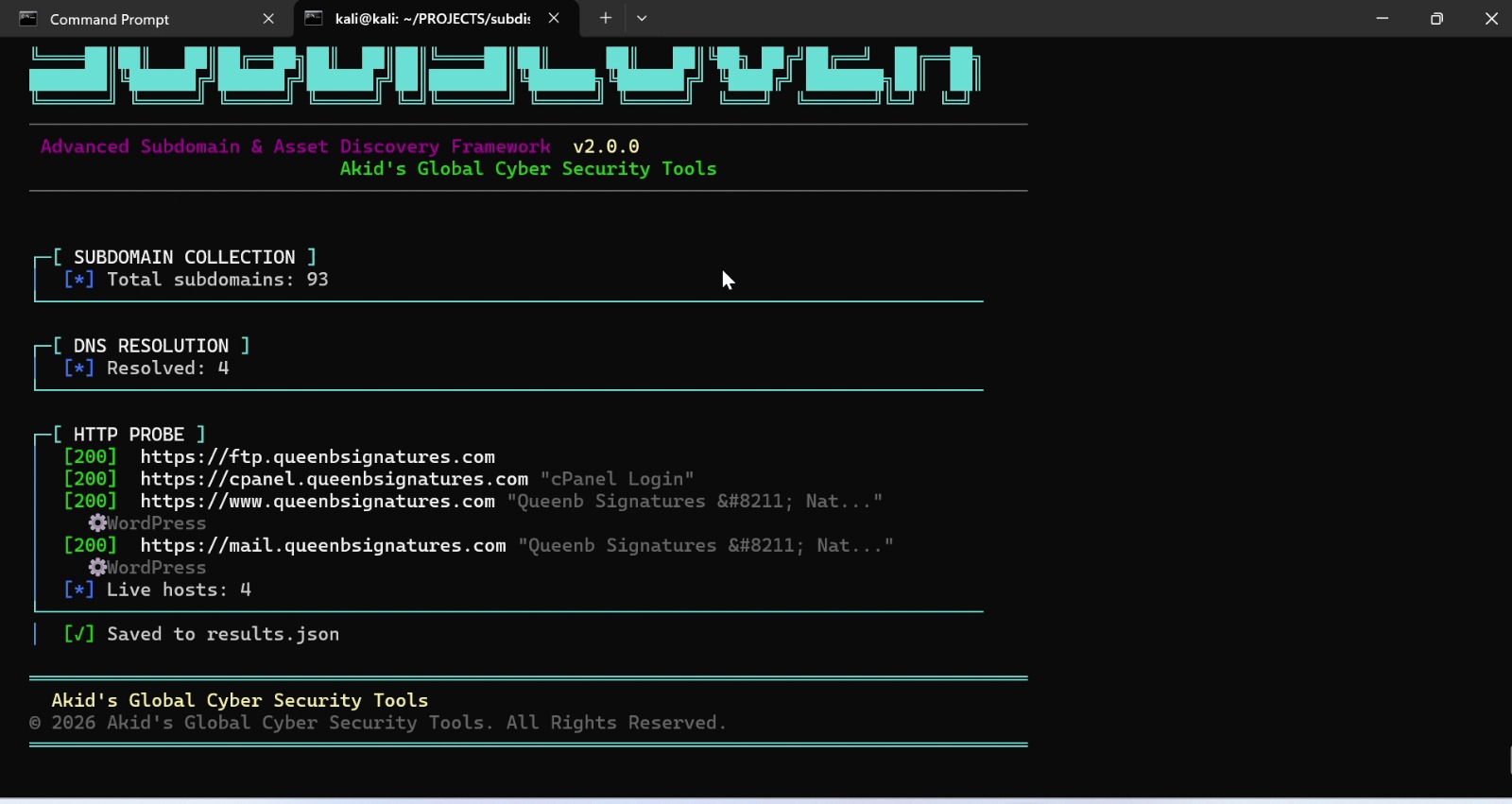
SubDiscover v2.0 is an advanced subdomain and asset discovery engine written in Go, designed for authorized security testing. It combines multiple collection techniques including DNS...
Real-time threat intelligence aggregation platform collecting IOCs from multiple OSINT sources, correlating them against your infrastructure, and providing actionable alerts.
Comprehensive network forensics toolkit for capturing, analyzing, and correlating network traffic to detect intrusions, lateral movement, and data exfiltration attempts.
Automated web application vulnerability scanner checking for OWASP Top 10 vulnerabilities, generating detailed reports and integrating with bug bounty platforms.
Enterprise security audit platform providing automated compliance checking against ISO 27001, NIST, SOC2, and PCI-DSS frameworks with executive-level reporting.
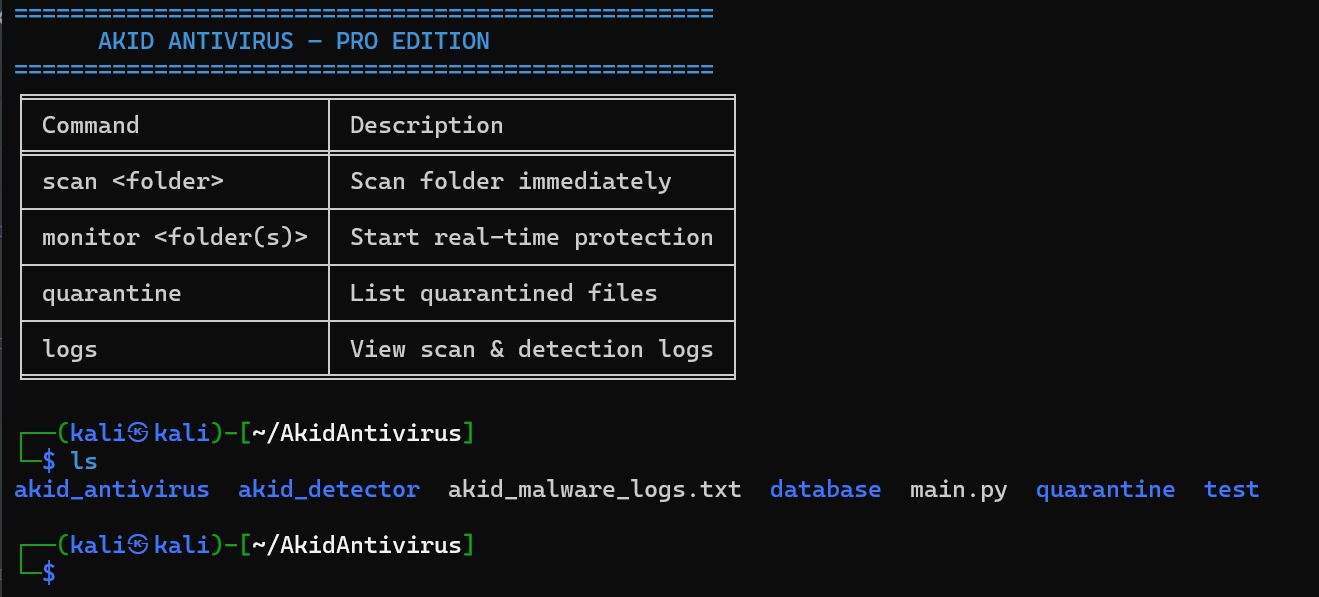
AKID Antivirus - Pro Edition is a lightweight, CLI-driven security tool designed for Linux environments, offering on-demand scanning and persistent real-time protection. Users can immediately...
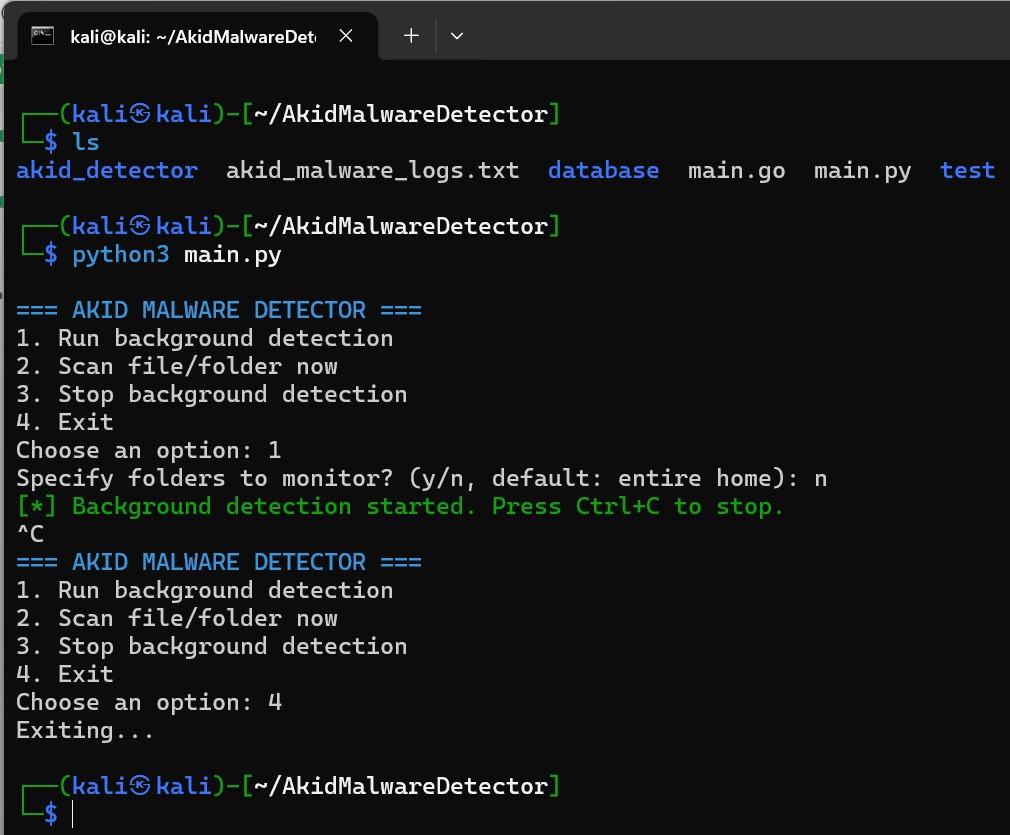
AKID Malware Detector is a cross-platform, CLI-based antimalware tool written in Python and Go, designed for proactive threat detection on Linux systems. It offers a...
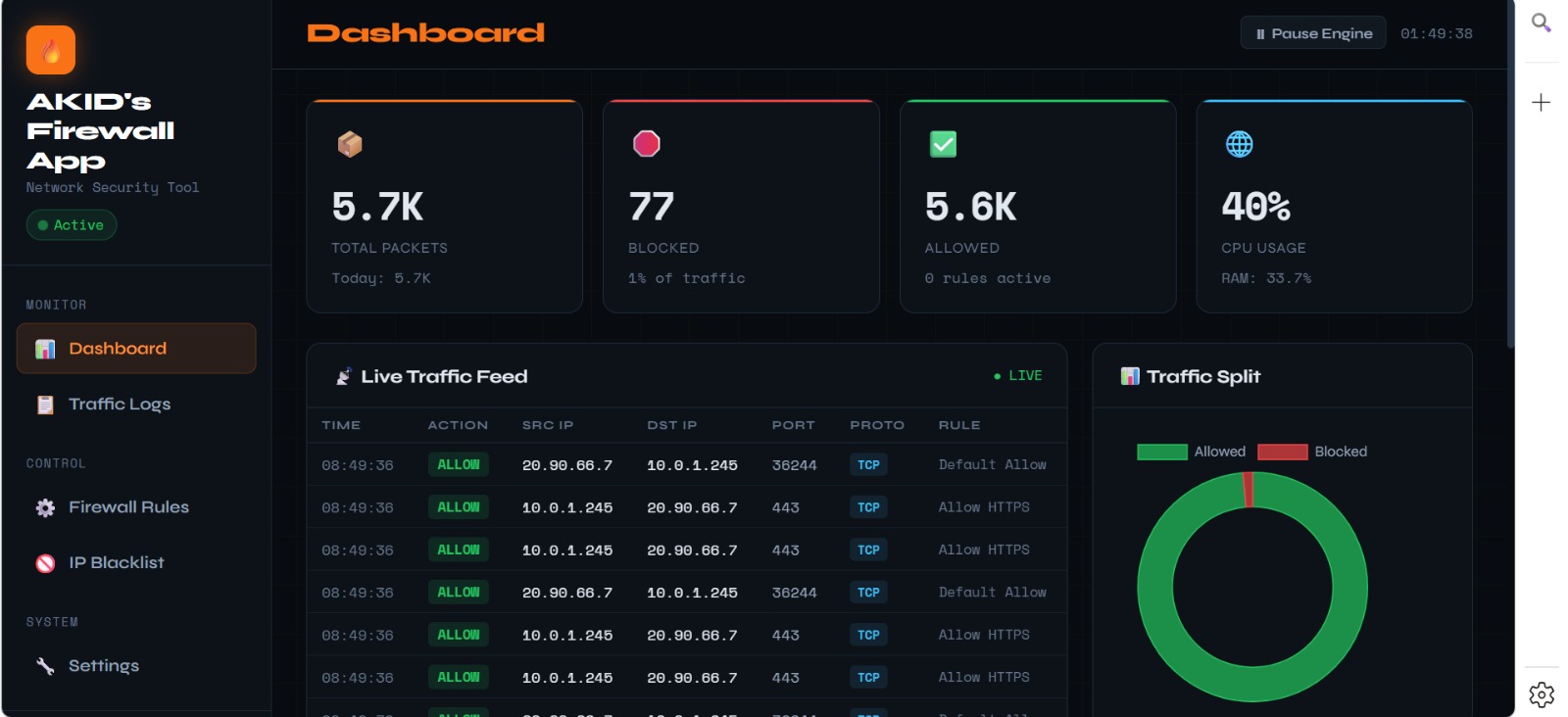
AKID's Firewall App is a cross-platform network security tool written in Python that provides real-time packet inspection, rule-based filtering, and a web-based dashboard accessible at...
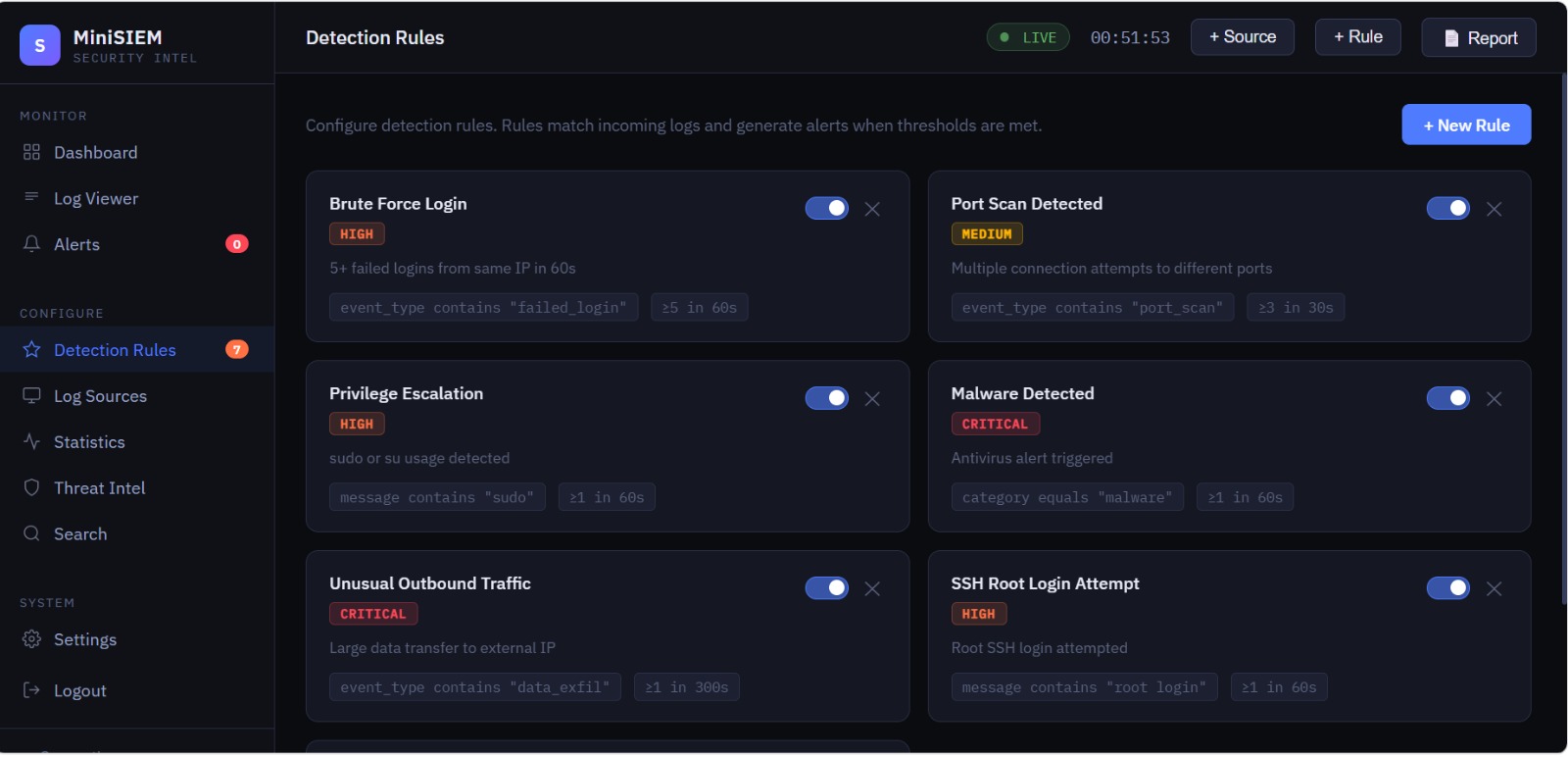
A lightweight, real-time Security Information and Event Management (SIEM) tool with a web dashboard, log analysis, detection rules, and alert management.
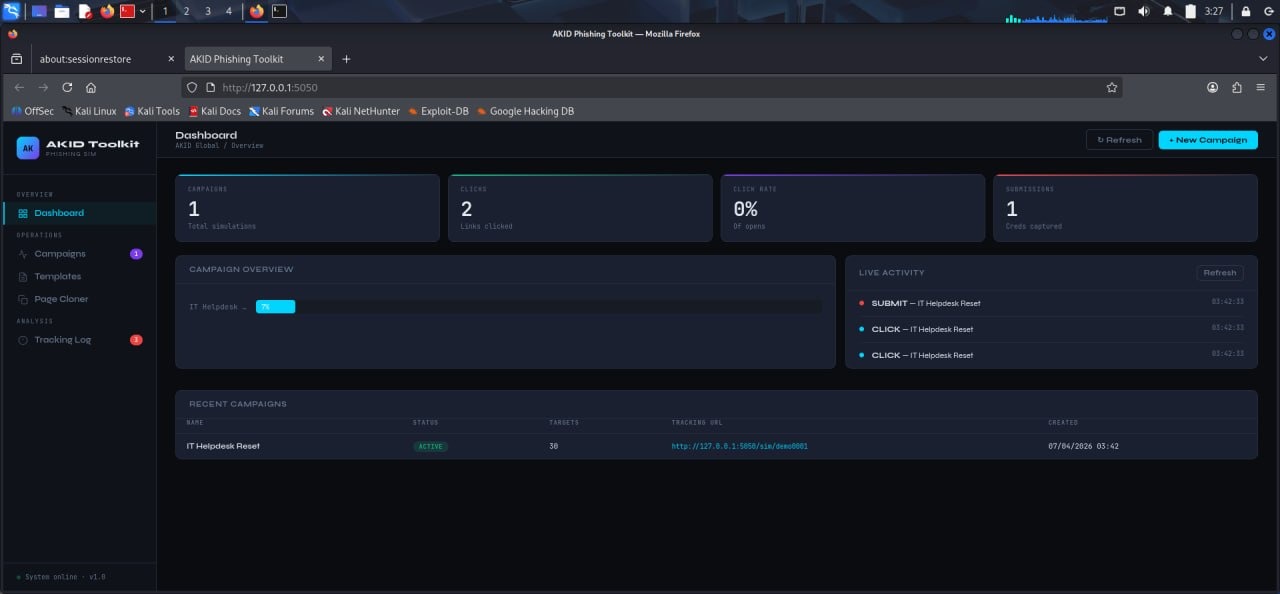
This tool is for authorized security testing only. Only use against systems you own or have explicit written permission to test. Every cloned page includes a visible...
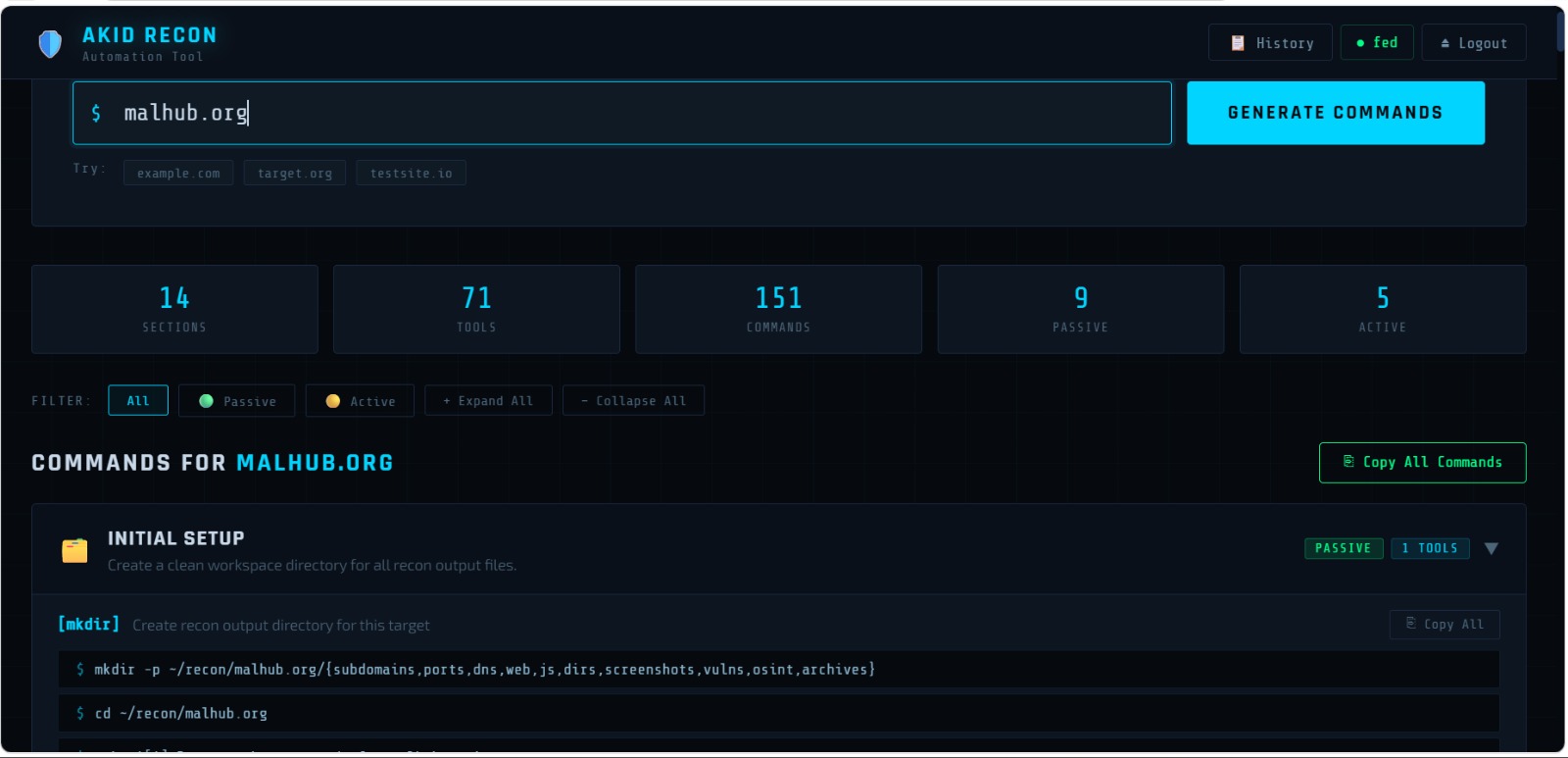
AKID's Recon Automation Tool is a web-based reconnaissance automation platform designed for cybersecurity professionals and penetration testers. Instead of manually typing complex terminal commands, users...
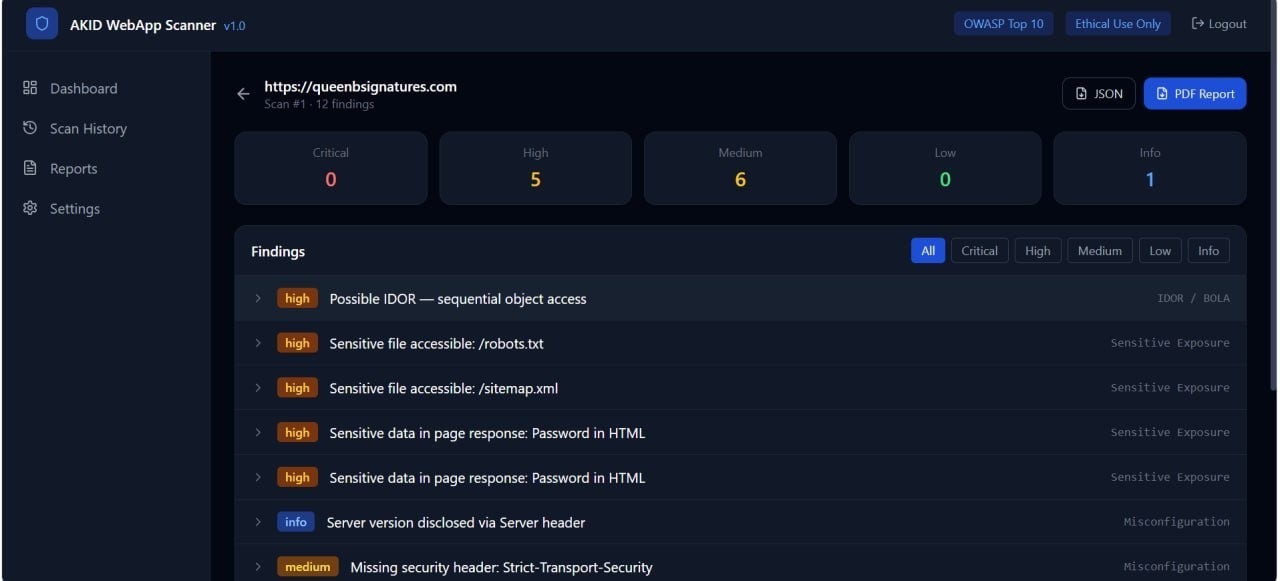
AKID WebApp Scanner is a full-stack web application vulnerability scanner covering the OWASP Top 10.

The File Encryptor is a robust security tool designed to protect sensitive data at rest by implementing strong, industry-standard encryption directly at the file level....
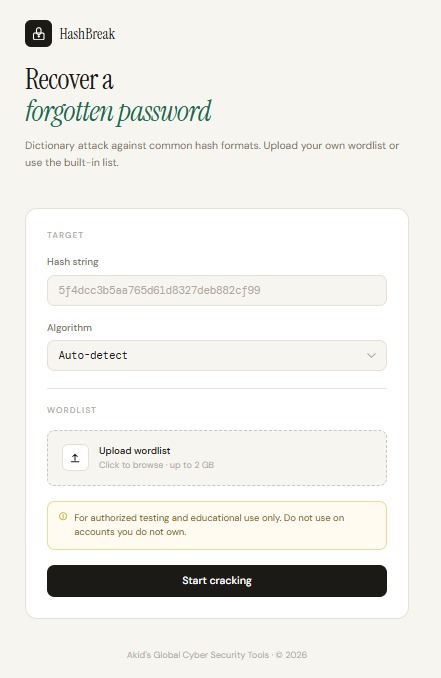
The HashBreak is an advanced security assessment tool designed for ethical penetration testing and password policy auditing. Unlike malicious crackers, this tool is built with...
An automated malware analysis framework combining static and dynamic analysis to identify, classify, and report on malicious code. Integrates with VirusTotal, Hybrid Analysis, and custom...
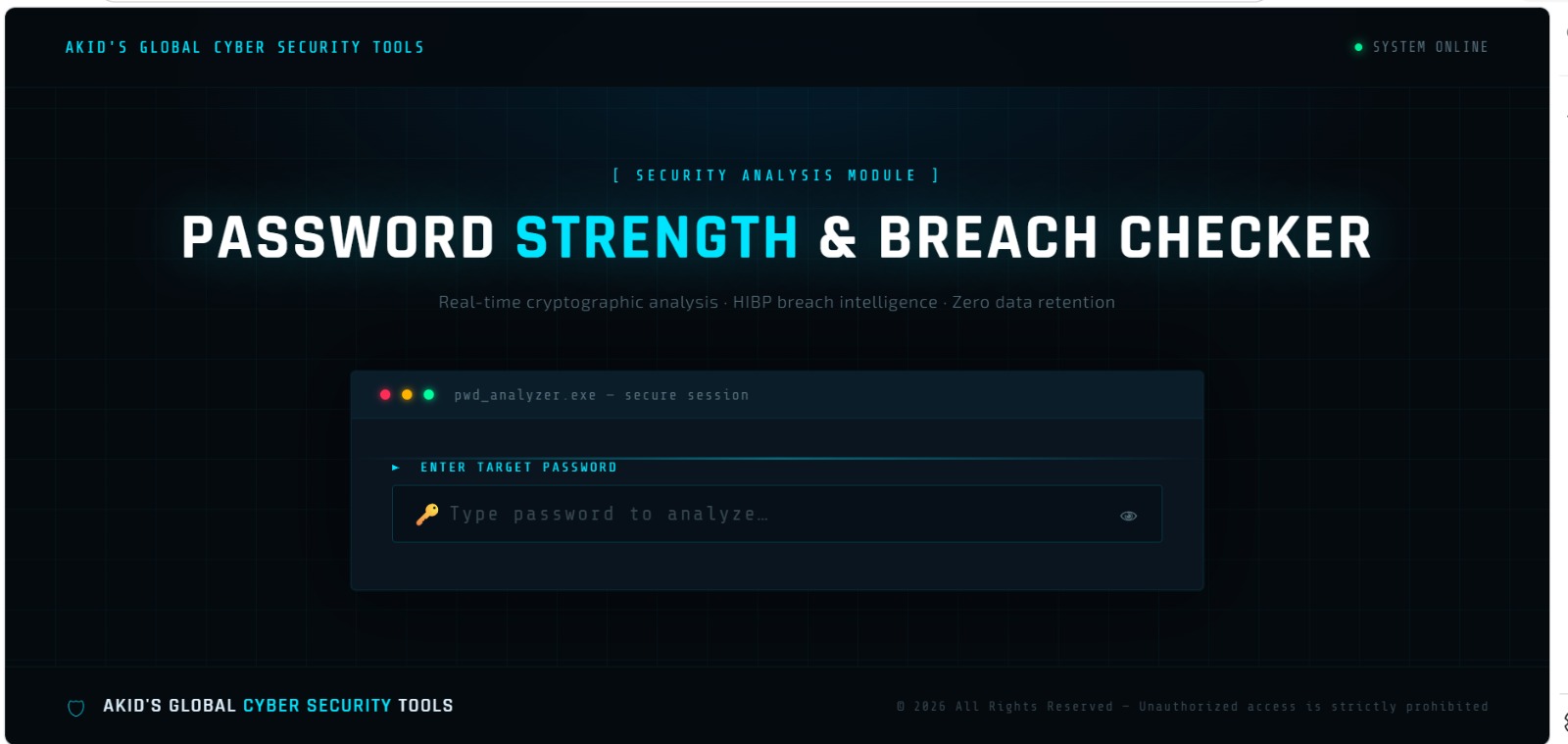
Password Strength and Breach Checker is a Python-based security tool that helps users create and validate strong, safe passwords. It evaluates password strength based on...
At 02:47 UTC, our SIEM detected unusual file modification patterns consistent with ransomware activity. This post-mortem documents our response process...
Read MoreEndpoint Detection and Response (EDR) tools have become increasingly sophisticated. This article explores techniques used in authorized penetration tests to evaluate EDR effectiveness...
Read MoreEmotet has evolved significantly since its first appearance in 2014. In this deep dive, we analyze the latest variant's evasion techniques, persistence mechanisms, and C2 infrastructure...
Read MoreWhether you need a full security audit, incident response, or malware analysis — let's talk.